What are BLE Beacons?
 BLE stands for Bluetooth Low Energy and is a part of the Bluetooth V4 protocol.
BLE stands for Bluetooth Low Energy and is a part of the Bluetooth V4 protocol.
Bluetooth is a wireless technology standard for exchanging data over short distances (using short-wavelength UHF radio waves in the ISM band from 2.4 to 2.485 GHz). Bluetooth devices comply with the Bluetooth SIG standard.
Bluetooth low energy (Bluetooth LE, BLE, marketed as Bluetooth Smart) is a power-friendly version of Bluetooth wireless technology perfect for devices needing to run off a small battery for long periods.
BLE allows Bluetooth devices to broadcast or receive tiny and static pieces of data within short distances. In simplistic words, it consists of two parts: a broadcaster (beacon device) and a receiver (smartphone + app).
Smartphone apps detect the BLE signal from a beacon and calculate the approximate distance to the beacon and act on the specific location – like presenting content to the smartphone user
For a general overview of indoor location technologies, check out our blog post “Indoor Positioning Systems based on BLE Beacons – Basics”.
What’s the difference between BLE and iBeacons?
![]() iBeacon™ is a trademark registered by Apple and refers to how Apple’s iOS devices detect beacons. Apple was the first smartphone manufacturer to include BLE in their iOS operating system as iBeacon which is a software extension of the BLE protocol. While BLE defines the data transmitted and the RSSI signal strength, iOS calculates the actual distance and delivers to the application the calculated values so the developer does not have to rely on RSSI calculations. Android programmers don’t have that luxury and have to base their distance calculations on the RSSI signal which can vary depending on the manufacturer of the device.
iBeacon™ is a trademark registered by Apple and refers to how Apple’s iOS devices detect beacons. Apple was the first smartphone manufacturer to include BLE in their iOS operating system as iBeacon which is a software extension of the BLE protocol. While BLE defines the data transmitted and the RSSI signal strength, iOS calculates the actual distance and delivers to the application the calculated values so the developer does not have to rely on RSSI calculations. Android programmers don’t have that luxury and have to base their distance calculations on the RSSI signal which can vary depending on the manufacturer of the device.
At the hardware level, beacons are BLE devices broadcasting data. At the software level, beacons are messages sent by broadcasting devices, that are then detected and processed by receiver devices, like a mobile app running on iOS. These data are considered beacons as well, depending on how you name things.
What information does the BLE Beacon send?
The beacons send the same package of information every n milliseconds. 350ms interval is what we use for our beacons and is often the default setting. The shorter the interval, the shorter the battery life, but the faster the device can be discovered. The beacon signal is a one-way discovery mechanism so the beacons are not aware of the phones, only the phones are aware of the beacons.
The data transmitted by the beacon includes the beacon identifier which consists of a long string called UUID, and two numeric values from 0-99999 for the beacon’s major and minor numbers. The UUID, major and minor number combinations are unique for each beacon and used for identification.
The beacon identity (UUID, major and minor number), interval, and signal strength are normally set by the manufacturer but they can be changed by an administrator who has the beacon’s password.
What are some practical apps for BLE Beacons?
Applications can utilize beacons for indoor positioning by reading the proximate distance to individual beacons and act on that information. For example, by presenting certain content for this location.
There are many kinds of applications utilizing beacons. What they have in common to display content or perform a location-specific operation. For example,
- shopping apps displaying promotions specific to what is in front of the customer
- point of sale payment applications and shopper loyalty programs
- tracking a user’s location, like a waiter doesn’t have to enter the table number when taking the order because there is a beacon under the table.
- guided indoor tours for museums exhibits where the user can get content about the artifacts in front of him
Locatify utilizes BLE beacons to bring an Automatic Museum Guide app to the guest with audio, and formatted content like texts and pictures.
What devices support BLE?
 Apple has support for BLE ever since iPhone4S and iPad2. Almost all Android devices developed manufactured since 2012 support BLE if they run Android 4.3 or later.
Apple has support for BLE ever since iPhone4S and iPad2. Almost all Android devices developed manufactured since 2012 support BLE if they run Android 4.3 or later.
Android 5 beacon scanning does behave differently from Android 4.x as it may appear to be slower. That is because, in Android 5, the beacon reading is done in predefined 2-5 second intervals.
Many other devices support BLE although they are not the topic of this discussion.
Where to get beacons and how much are they?
There are many BLE beacon manufacturers who package and price their beacons differently and use different antennas. There are only a few chipset makers (the BLE chip inside the beacon) and many manufacturers use the same chipset.
The chipsets made today come from Texas Instruments, Nordic Semiconductor, Dialog Semiconductor, and CSR. Here is more information about the chipset makers.
Battery lifetime may vary between providers and signal strength. The most common battery lifetime is 1-2 years.
We at Locatify have used Kontakt.io and Estimote beacons. They both use the same chipset but package them differently. Kontakt.io beacons are plain and durable with a replaceable CC battery, while Estimote beacons are in a designer-made casing for show.
Price per beacon varies from 20 – 30 Euros per beacon depending on manufacturer and quantity ordered.
Proximity detection — accuracy and limitations
The proximity distance to a beacon is calculated and the accuracy of the calculation gets worse the further away from the beacon the device is. Accuracy is the best when the device is less than 1 meter away. Between 2-7 meters range the accuracy fluctuates +- 1.5 meters, and beyond that, the accuracy will not be good enough for distance calculation in our experience.
It’s also common to use only four possible values for proximity. The values from shortest to longest distance are: immediate (<≈ 1m), near (<≈10m), far (<≈40m), unknown.
The device scans for beacons in 3-second intervals and sometimes a beacon is not caught in the first scan, but is in the second scan and then it takes 6 seconds for the beacon to be discovered. It’s good to have at least 2 beacons at each station if quicker detection is critical.
Installation
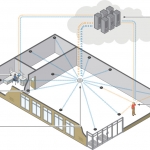
![]() The beacon signal will be lost if it is blocked by metal, water, or the human body. For that reason, it is good to place the beacons above 2.5 meters high on walls or on the ceiling if the ceiling is not higher than 3-4 meters.
The beacon signal will be lost if it is blocked by metal, water, or the human body. For that reason, it is good to place the beacons above 2.5 meters high on walls or on the ceiling if the ceiling is not higher than 3-4 meters.
If blocking by other guests is not an issue, then the beacon can be placed at or under the object for display as well. For example, if a new content is activated when the guest is standing in front of a cabinet with a beacon configured to activate at “near” proximity.
The Locatify Creator CMS tool has been developed to make the installation as easy as possible so non-technical people can actually perform the installation, configure the beacons, content, and maintain the installation.
When the content is ready, then the actual installation of the beacons can take less than a day for setting up 10 stations or so. With the admin app, it’s possible to test the beacons and find the best location for them.
Check out our “Developer Story; The first indoor location experience” blog post from 2014 when we did the first installation at Eldheimar. This is when we learned all the complexities and after this installation, we could make the best CMS system to manage the beacons and content easily.
Maintenance
 The content can be changed at all times using the Locatify Creator CMS tool, new venues defined, and beacons added or moved.
The content can be changed at all times using the Locatify Creator CMS tool, new venues defined, and beacons added or moved.
The beacon’s battery will eventually run out or the beacon can accidentally be detached for some reason. Therefore it is necessary to regularly walk through the venue with our app in “admin” mode and see if all beacons are responding and the battery level is acceptable.
Kontakt.io offers an Admin app for maintaining the beacon’s firmware and checking the battery. The app is available for Android and iOS.
Trends
Eddystone Beacons
Google introduced the EddyStone protocol for BLE beacons in 2015 and most manufacturers have included the Eddystone specification in the beacon firmware. The Eddystone specification adds a number of broadcast frame types, including Eddystone-URL, the backbone of the Physical Web.
With the Eddystone, the beacon sends the URL to the app which then opens a page on a device.
Cloud Beacons
Cloud beacons use built-in Wi-Fi and can be used to monitor other Bluetooth beacons and send data over the internet. This is a very powerful feature as it allows you to easily access data gathered from monitoring. Additionally, cloud beacons can track (MAC address and distance) any WiFi-enabled device in the proximity and backup data, settings, and configuration of all beacons on site.
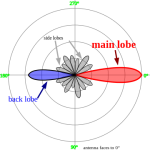
Directional Beacons
Most of the beacons currently available are omnidirectional which means that they radiate UHF waves uniformly in all directions. In Surtsey museum, we had to limit the radiation of certain beacons to a relatively small area to achieve the best performance. We used a cone-shaped metal in which we inserted the basic beacons from Kontakt.io. This improvised solution did cause a mild directional effect. There are also vendors that offer directional beacons. For example, Gimbal’s Beacon Series 21 is equipped with a coaxial plug thus making it possible to attach the external directional antenna.
Security
The biggest security concern about BLE beacons is related to the beacon profile. There are several apps available that can detect information about the beacons nearby (major number, minor number, and UUID). This allows others to clone your beacon and use it in a different location or to use your beacon in their own app.
Another security risk is that beacons can be stolen. To avoid this, we usually place them on the ceiling or high on the walls thus making them hard to reach.
Useful links
- Create a beacon-enabled app project using Locatify’s Creator CMS
- Video Tutorial for creating an indoor guide app using beacons
- Talk to sales about getting your own custom app